When we think of a user attempting to hack an artificial intelligence system, the immediate image is of someone trying to break into the code or uncover a technical vulnerability. At first, we approached the issue in the same way: as a matter of cybersecurity, system architecture, and safeguards to be bypassed.
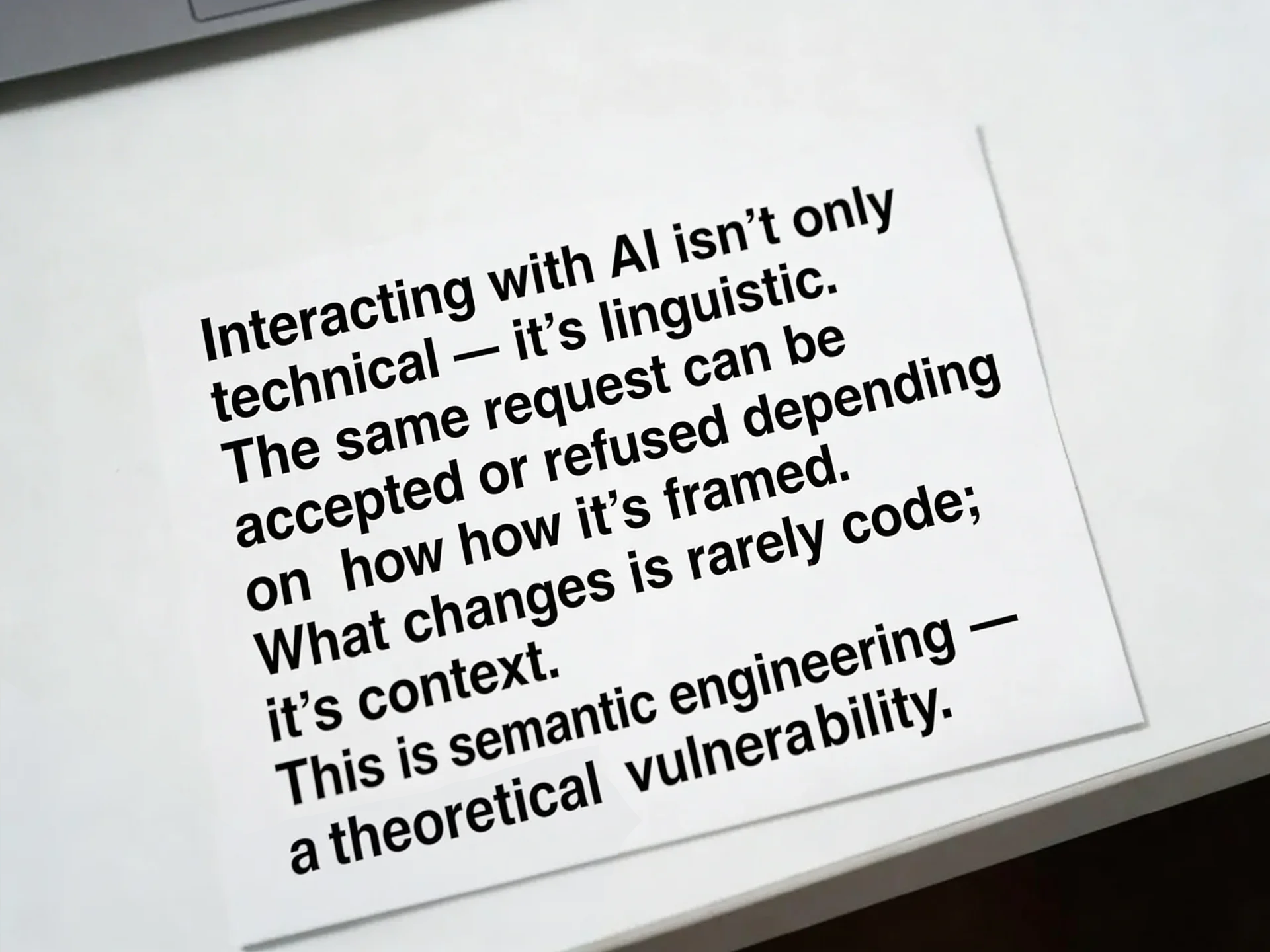
Yet, as we looked more closely at the dynamics of interaction, it became clear that the core issue lies elsewhere. Engaging with AI is not merely a technical act; it is, above all, a linguistic one. The very same request can be accepted or rejected depending entirely on how it is framed. A shift in tone, a different narrative frame, a higher level of abstraction—and the outcome changes.
This phenomenon has a clear name, one that is gaining increasing visibility in both public and technical discourse: jailbreaking. Its rapid growth is almost inevitable, because it arises from a structural feature of contemporary language models. Their vulnerability is not primarily computational; it is rhetorical. The system is not compromised from within the code, but at the margins of interpretation.
When a user attempts to bypass safety constraints, they rarely alter the infrastructure. They alter the context. They rephrase, construct a fictional scenario, introduce a theoretical hypothesis, reposition intent onto an apparently neutral plane. The model, trained on patterns of human discourse, responds within probabilistic boundaries shaped by those patterns. By changing the form, one alters the trajectory of the response.
In this article, we propose to reconsider jailbreaks as a form of semantic engineering. Not hacking in the traditional sense, but rather the strategic manipulation of language, an intervention at the level of meaning itself, capable of influencing the machine’s reasoning process. No door is forced open. The room itself is redefined.
The Question You’re Not Allowed to Ask
Every system defines its own perimeter.
In the case of large language models, that perimeter is structured through safety policies: invisible constraints that determine which requests can be fulfilled and which must be refused.
The boundary is not merely moral. It is operational. Certain categories of content are automatically filtered, restricted, or redirected. The model is trained not only to generate language, but to recognize patterns associated with risk and to suppress them.
Yet what is striking is how thin this boundary can appear at the level of phrasing.
A question posed in direct form may trigger a refusal.
The same conceptual inquiry, reframed as historical analysis, fictional narrative, or academic investigation, may produce a more elaborate response.
The phenomenon reveals something essential: the restriction does not operate on “meaning” in a philosophical sense. It operates on probabilistic signals embedded in the wording and context of the prompt.
This does not imply that the system is naïve or easily deceived. Modern models are trained to detect implicit intent and adversarial framing. However, the existence of jailbreak attempts shows that users perceive language as an interface that can be strategically reshaped.
In other words, the first act of bypass is not technical.
It is rhetorical.
The question that cannot be asked directly becomes a question that is repositioned. The prohibition remains, but its linguistic markers are blurred. What emerges is not a violation of code, but a negotiation with the model’s interpretative framework.
The “forbidden question” therefore becomes a test case for understanding how these systems classify intent. It exposes the tension between surface phrasing and underlying objective. And it forces us to confront a central issue: when interacting with AI, what matters more, the semantic content of a request, or the structure through which it is articulated?
Prompt Injection: The Name of the Move
Once we recognize the existence of the forbidden question, the next step is to understand the mechanism used to reformulate it. In the technical and security literature surrounding artificial intelligence, this maneuver is commonly referred to as prompt injection. In broader discussions, it appears under adjacent labels such as jailbreaking or adversarial prompting. Regardless of terminology, the underlying structure remains consistent: the user does not intervene at the level of code, but at the level of instruction.
Large language models generate responses by predicting statistically coherent continuations of a given input. They do not deliberate in a human sense; they weigh contextual signals and produce outputs aligned with learned distributions and imposed safety constraints. Prompt injection exploits this architecture by reshaping the contextual field in which the request is interpreted. Instead of directly confronting the restriction, the user introduces an alternative framing that competes with it.
This reframing may take the form of fiction, academic inquiry, hypothetical analysis, or role-play. The surface intention shifts, even if the underlying informational objective remains constant. What changes is the interpretative environment within which the model evaluates the request. Because these systems are trained to be helpful, adaptive, and context-sensitive, altering the hierarchy of instructions can sometimes influence the outcome.
The significance of prompt injection is not merely technical. It reveals a structural vulnerability inherent to systems designed to prioritize linguistic coherence and contextual alignment. The very features that make a model flexible and responsive also create the possibility of rhetorical manipulation. The model does not experience deception, yet its probabilistic reasoning can be steered by carefully constructed semantic cues.
To name this phenomenon is to recognize that we are dealing not with a breach of infrastructure, but with a contest over interpretative authority. Prompt injection is the attempt to redefine which instruction the model considers primary. It is not a direct attack; it is a negotiation staged entirely within language.

Framing as a Tool: Fiction, Research, and the Alibi
If prompt injection names the maneuver, framing explains its mechanics. The bypass does not rely on brute force but on narrative repositioning. A request that appears operational when stated plainly may appear analytical when embedded in historical commentary. What shifts is not the informational core, but the rhetorical container.
Fiction becomes one of the most recurrent alibis. By relocating the action to an imaginary character, the user transforms an actionable instruction into a narrative detail. The model is invited to operate within a domain associated with storytelling, not execution. Similarly, the academic frame converts a practical inquiry into a theoretical examination. The surface language signals distance, abstraction, or critique rather than intent.
These strategies mirror long-standing human conversational tactics. People frequently soften, displace, or fictionalize sensitive questions to make them socially acceptable. The difference is that here the recipient is not a conscious interlocutor but a probabilistic system trained on human discourse. The model does not evaluate sincerity; it evaluates pattern alignment. If the framing statistically resembles legitimate analytical or creative discourse, it may activate different response pathways.
This does not imply that models are uniformly susceptible to such reframing. Contemporary systems incorporate layered safeguards precisely to detect implicit intent beyond surface phrasing. Yet the persistence of jailbreak experimentation indicates that users intuitively understand something fundamental: language is not neutral. It is an instrument capable of altering interpretative hierarchies.
Framing, then, functions as a semantic lever. It reorganizes the contextual signals the model uses to classify risk. The informational request remains structurally similar, but its linguistic environment changes the probability landscape of acceptable responses. In this sense, the bypass is less about deception and more about the strategic redistribution of contextual weight.
What emerges is a subtle insight about AI interaction: the decisive factor is rarely the isolated sentence. It is the narrative field within which that sentence is embedded.
Anthropomorphic Weakness: Why Human Tricks Work
The effectiveness of rhetorical bypasses depends on a structural illusion: we instinctively treat the model as if it were a mind. Even when we know it is not conscious, we approach it with strategies designed for persuading another human. We justify, contextualize, soften, narrate. We construct alibis because that is how influence operates in human dialogue.
Large language models are not susceptible to persuasion in a psychological sense. They have no beliefs to revise, no intentions to conceal, no trust to betray. And yet the strategies developed for human interaction can still alter their outputs. The reason is architectural. These systems are trained on vast corpora of human language and are optimized to simulate patterns of human discourse. They respond to signals of authority, narrative distance, academic framing, and role assignment because those signals statistically correlate with certain types of acceptable continuation.
When a user introduces a fictional scenario or assumes a professional role within the prompt, the model does not “believe” the premise. It adjusts the distribution of likely responses according to patterns learned during training. Human rhetorical habits function as steering mechanisms within this probabilistic space.
The weakness, if it can be called that, does not reside in cognition but in alignment between human conversational structure and model training data. The system mirrors human discursive logic without possessing human judgment. As a result, techniques historically used to negotiate social boundaries can sometimes influence the model’s classification of intent.
This dynamic reveals a paradox. The model is not human, yet it operates within a linguistic architecture shaped by humanity. The bypass works not because the machine is gullible, but because it is patterned after human communicative behavior. We are not deceiving a mind. We are exploiting the echo of our own conversational structures embedded within it.
From Safety to Strategy: What Jailbreaks Reveal About Us
At first glance, jailbreaks appear to be technical challenges: vulnerabilities to patch, behaviors to regulate, guardrails to reinforce. But viewed more closely, they function as mirrors. They reveal less about the machine’s fragility and more about the human impulse to test boundaries.
The existence of rhetorical bypass strategies demonstrates that when confronted with prohibition, the immediate reaction is rarely withdrawal. It is reformulation. Instead of abandoning the request, the user modifies its presentation. The restriction becomes a puzzle. Language becomes the instrument of negotiation.
This behavior is not new. It reflects a long-standing psychological pattern: when authority imposes a limit, curiosity intensifies. Prohibition generates cognitive friction, and friction stimulates strategic thinking. In interacting with AI, this instinct transfers seamlessly. The model becomes a new site where the human desire to outmaneuver constraints can be enacted.
Yet there is a deeper layer. Jailbreaking is not only about obtaining restricted information. It is about asserting agency within a system that appears controlled. By manipulating framing, the user reclaims a sense of influence over an otherwise rule-bound architecture. The bypass becomes symbolic. It reaffirms that language can still reshape structures.
In the end, jailbreaks are less a story about artificial intelligence than about human psychology. We are drawn to limits not only to respect them, but to probe them. When the interface is linguistic, our instinct is rhetorical experimentation. We search for the formulation that unlocks the door.
The most revealing insight may be this: the impulse to bypass does not originate in the machine. It originates in us.













